The Active Directory Recycle Bin is disabled by default. In order to use it to restore deleted objects, you must enable it. You cannot restore any objects deleted before Recycle Bin was enabled. Note that Recycle Bin can be enabled only once without a possibility to disable it afterwards.
Prerequisite: Enable the Recycle Bin in Active Directory
- Open the Server Manager management console -> Click Tools -> Active Directory Administrative Center
(Alternatively: Open the “run” box (click Start -> Run or use the Win-R keyboard shortcut) -> Type dsac.exe -> Click OK.) - Click on your domain name. In the Tasks pane, click Enable Recycle Bin.
- In the confirmation window, click OK.
Restore an Object with the Active Directory Administrative Center (ADUC)
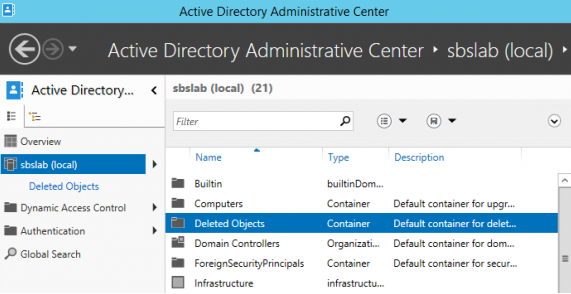
- Open the Server Manager management console -> Click Tools -> Active Directory Administrative Center
(Alternatively: Open the “run” box (click Start -> Run or use the Win-R keyboard shortcut) -> Type dsac.exe -> Click OK. - In the left pane of the ADUC,select the domain in which the deleted object resided. In the center pane, select the Deleted Objects container:
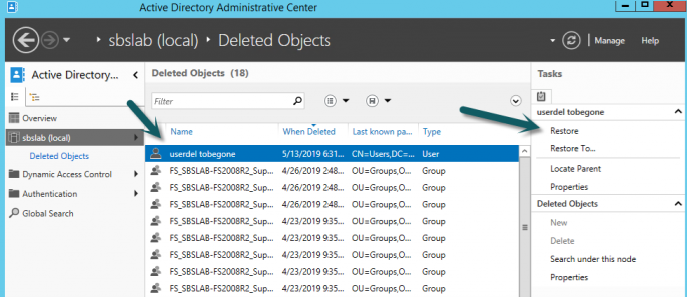
- Select the deleted object. Then do one of the following:
- To restore the object to its original container, click Restore:
Restore an Object using PowerShell
Alternatively, you can restore an AD object using the Restore-ADObject PowerShell cmdlet:
Get-ADObject -Filter {displayName -eq "userdel tobegone"} -IncludeDeletedObjects | Restore-ADObject
- Open Netwrix Recovery for Active Directory -> Select the object you want to restore (to locate it quickly, use the search function on the left):
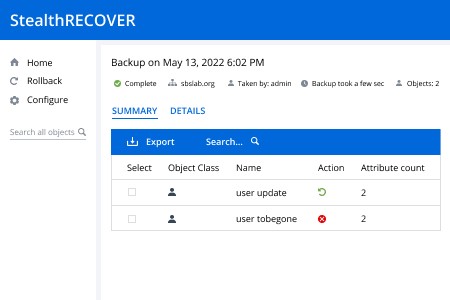
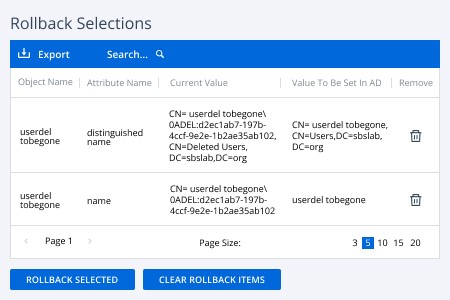
- Select the object, or the attributes of the object that you want to roll back:
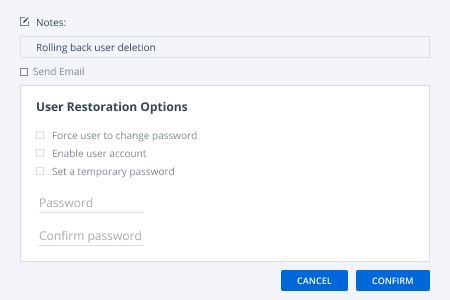
- Optionally, provide a note about the operation (such as why it was needed) and set the following options:
- Force the user to change the account’s password at the next login.
- Enable the user account.
- Assign a specific new password to the account.